Practically overnight organisations have been forced to work remotely.
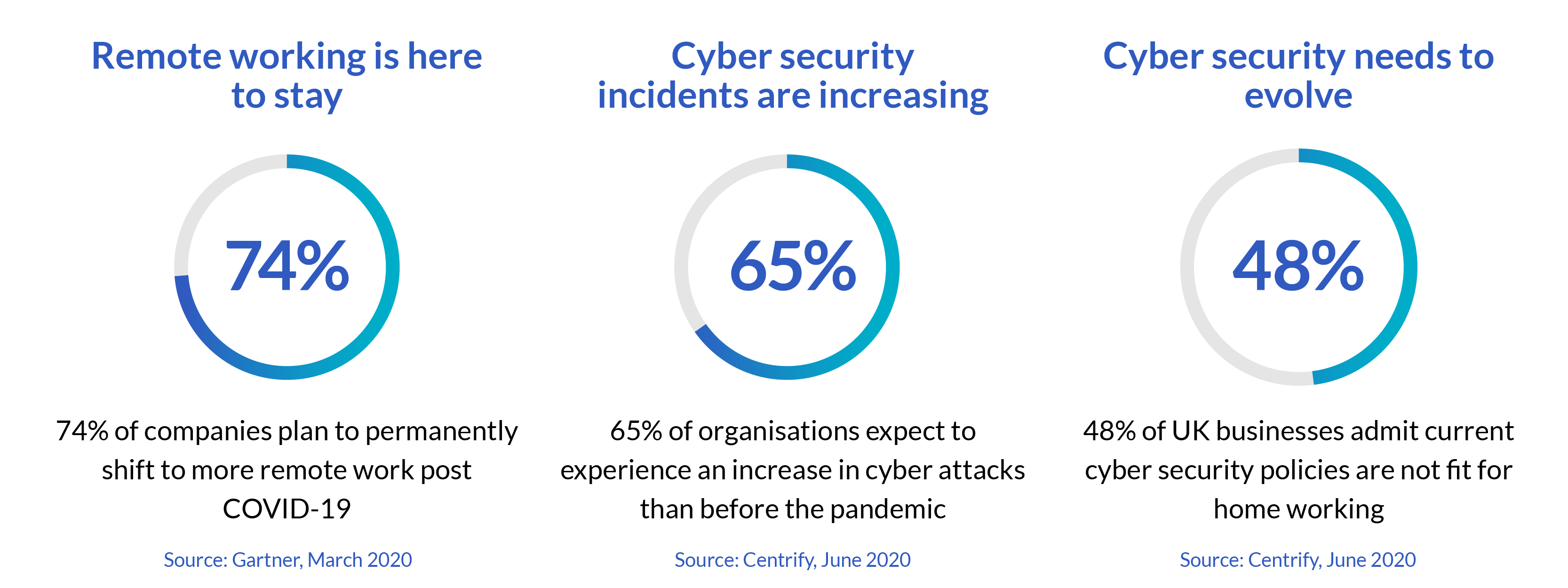
What began as a short-term necessity is now being considered a longer-term solution with a recent Gartner survey revealing 74% of organisations surveyed intend to shift some staff to permanent remote working following COVID-19.
Remote working has been on the rise for years thanks to its flexibility, work-life balance, and increased productivity; however, the current pandemic has acted as a catalyst to accelerate mass adoption. Now widespread, it will be difficult for organisations to return to exactly how they were before as staff enjoy these benefits and business leaders consider the cost savings of reducing office space.
With more permanent remote (or flexible) working currently being considered across the UK, organisations are having to review how to make this sustainable. Initial solutions that were launched to support remote working, such as Microsoft Teams, have been successful for business continuity and collaboration but one critical element has fallen behind: cyber security.
The sudden transition to remote working has meant that former cyber security models are no longer fit for purpose and staff identities, devices and data are susceptible to cyber-attacks. In fact, nearly half of UK businesses believe that their cyber security is unfit for permanent remote working according to a recent report from Centrify. As cyber-attacks continue to increase and capitalise on the new vulnerabilities of remote working, cyber security needs to be a top business priority.